![]()
We develop and market breakthrough IDPS technology for IVN authentication-encryption and firmware authentication augmented by CyberHealth monitoring. We provide safety, privacy and data integrity for connected vehicles with our patented, multi-layered embedded software solutions.
Official partners that help us to provide top-notch cybersecurity services: Landon TechnologiesFor more information visit trilliumsecure.com and follow us on

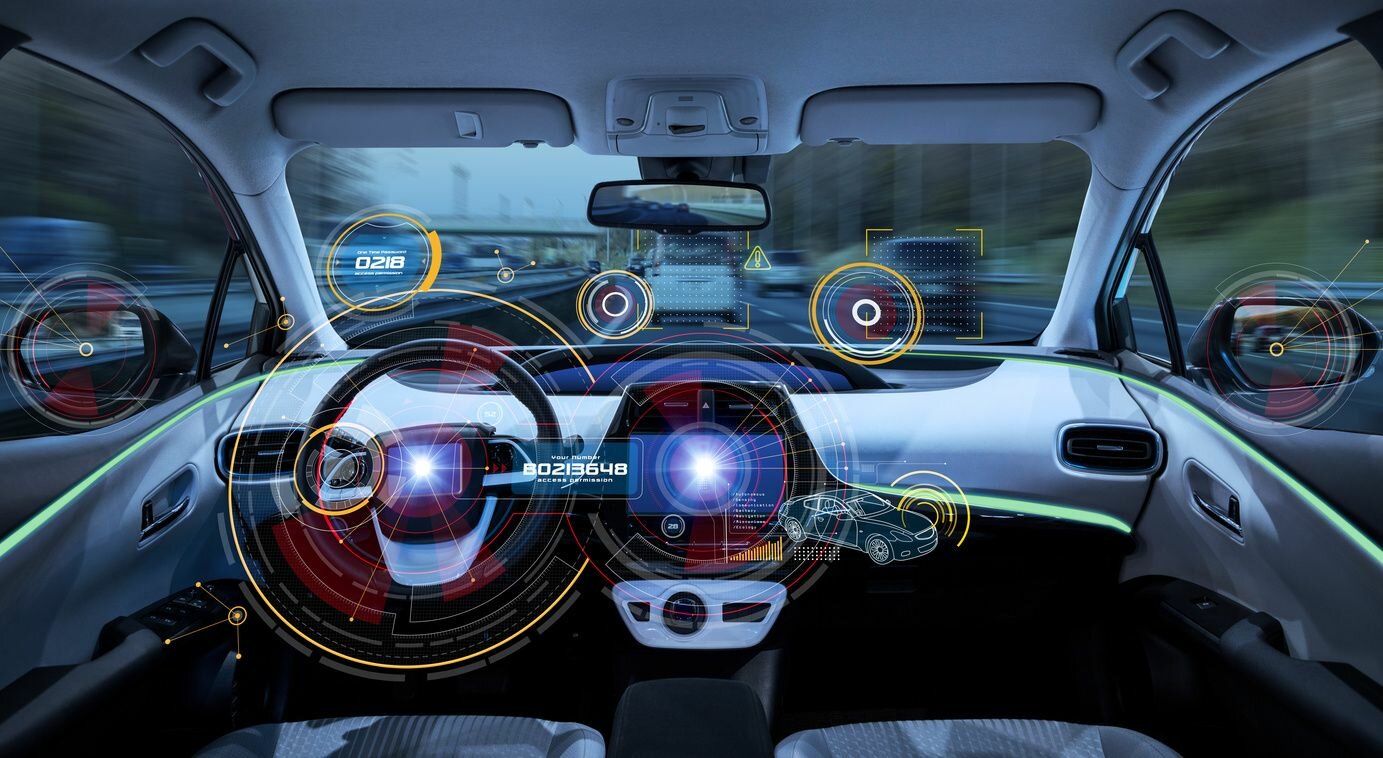









 In-Vehicle
In-Vehicle Firmware Authentication
Firmware Authentication Secured Updates
Secured Updates Multilayer IDPS &
Multilayer IDPS &